WordPress is one of the most popular website builders in the world because it offers powerful features and a secure codebase. However, this popularity makes it a target for DDoS attacks.
Hackers use DDoS attacks to slow down websites down and make them inaccessible to users. These attacks can target both small and large websites. The consequences of a DDoS attack can be severe, resulting in lost revenue, damaged reputation, and frustrated visitors.
WPBeginner has been the target of many of these attacks, and we have learned how to take steps to minimize the risk and keep our website safe. You may be wondering how a small business website using WordPress can prevent such DDoS attacks with limited resources.
This guide will show you how to prevent and stop DDoS attacks in WordPress, letting you confidently manage your website security against attacks like a total pro.

What Is a DDoS Attack?
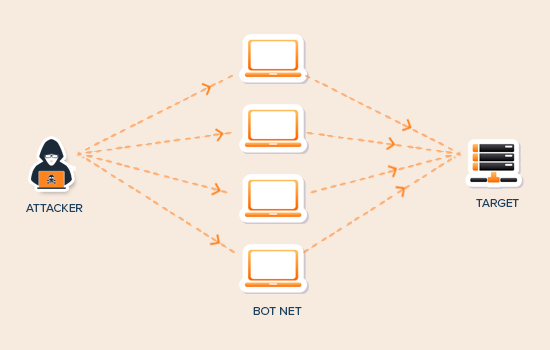
DDoS (Distributed Denial of Service) is a type of cyber attack that uses compromised computers and devices to send or request data from a WordPress hosting server. The purpose of these requests is to slow down and eventually crash the targeted server.
DDoS attacks evolved from DoS (Denial of Service) attacks. Unlike a DoS attack, they take advantage of many compromised machines or servers spread across different regions.
These compromised machines form a network, which is sometimes called a botnet. Each affected machine acts as a bot and launches attacks on the targeted system or server. This allows them to go unnoticed for a while and cause maximum damage before they are blocked.
Even the largest internet companies are vulnerable to DDoS attacks.
In 2018, GitHub, a popular code hosting platform, witnessed a massive DDoS attack that sent 1.3 terabytes per second of traffic to their servers.
You may also remember the notorious 2016 attack on DYN (a DNS service provider). This attack got worldwide news coverage as it affected many popular websites like Amazon, Netflix, PayPal, Visa, Airbnb, The New York Times, Reddit, and thousands of other websites.
DDoS FAQs
Here are some answers to frequently asked questions about DDoS attacks.
Why Do DDoS Attacks Happen?
There are several motivations behind DDoS attacks. Here are some common ones:
- Technically savvy people who are just bored find it adventurous
- People and groups making a political point
- Groups targeting websites and services of a particular country or region
- Targeted attacks on a specific business or service provider to cause monetary harm
- Blackmail in order to collect ransom money
What’s the Difference Between a Brute Force Attack and a DDoS Attack?

Brute force attacks try to gain unauthorized access to a system by guessing passwords or trying random combinations.
DDoS attacks are purely used to crash the targeted system, making it slow or inaccessible.
For more details, see our guide on how to block brute-force attacks on WordPress.
What Damage Can Be Caused by a DDoS Attack?
DDoS attacks can reduce a website’s performance or make it inaccessible. This results in a bad user experience, loss of business, and the costs of mitigating the attack, which can be thousands of dollars.
Here is a breakdown of these costs:
- Loss of business due to the inaccessibility of the website
- Cost of customer support to answer service disruption-related queries
- Cost of mitigating attack by hiring security services or support
- The biggest cost is the bad user experience and brand reputation
How Can I Stop and Prevent DDoS Attacks in WordPress?
DDoS attacks can be cleverly disguised and difficult to deal with. However, with some basic security best practices, you can prevent and easily stop DDoS attacks from affecting your WordPress website.
Here are the steps you need to take to prevent and stop DDoS attacks on your site:
Remove DDoS / Brute Force Attack Verticals
The best thing about WordPress is that it is highly flexible. WordPress allows third-party plugins and tools to integrate into your website and add new features.
To do that, WordPress makes several APIs available to programmers. These APIs are methods by which third-party WordPress plugins and services can interact with WordPress.
However, some of these APIs can also be exploited during a DDoS attack by sending a ton of requests. You can safely disable them to reduce those requests.
Disable XML RPC in WordPress
XML-RPC allows third-party apps to interact with your WordPress website. For example, you need XML-RPC to use the WordPress app on your mobile device.
If you are like a vast majority of users who don’t use the mobile app to run their website, then you can disable XML-RPC by simply adding the following code to your site’s .htaccess file:
# Block WordPress xmlrpc.php requests
<Files xmlrpc.php>
order deny,allow
deny from all
</Files>
For alternative methods, see our guide on how to easily disable XML-RPC in WordPress.
Disable REST API in WordPress
The WordPress JSON REST API allows plugins and tools to access WordPress data, update content, and/or even delete it. Here is how you can disable REST API in WordPress.
We recommend using the WPCode plugin. This is the best code snippets plugin that will enable you to disable the REST API in just a few clicks.
For more information, please see our guide on how to disable JSON REST API in WordPress.
Alternatively, you can use the Disable WP Rest API plugin. The plugin works out of the box and will disable the REST API for all non-logged-in users.
Activate a WAF (Website Application Firewall)
Disabling attack vectors like REST API and XML-RPC provides limited protection against DDoS attacks. Your website is still vulnerable to normal HTTP requests.
While you can mitigate a small DDoS attack by trying to catch the bad machine IPs and blocking them manually, this approach is less effective when dealing with a large attack.
The easiest way to block suspicious requests is by activating a website application firewall.
A website application firewall acts as a proxy between your website and all incoming traffic. It uses a smart algorithm to catch all suspicious requests and block them before they reach your website server.
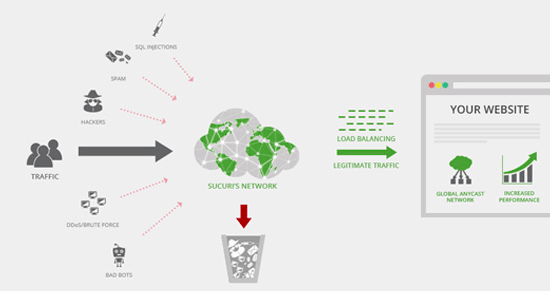
We recommend using Sucuri because it is the best WordPress security plugin and website firewall. It runs on a DNS level, which means it can catch a DDoS attack before it can make a request to your website.
Pricing for Sucuri starts from $199.99 per year.
We use Sucuri on WPBeginner. See our case study on how they help block hundreds of thousands of attacks on our website.
Alternatively, you can use Cloudflare. However, Cloudflare’s free service only gives limited DDoS protection. You’ll need to sign up for at least their business plan for layer 7 DDoS protection, which costs around $200 per month.
See our article on Sucuri vs. Cloudflare for a detailed side-by-side comparison.
Note: Website Application Firewalls (WAFs) that run on the application level are less effective during a DDoS attack. They block the traffic once it has already reached your web server, so it still affects your overall website performance.
Identify Whether It Is a Brute Force or DDoS Attack
Both brute force and DDoS attacks intensively use server resources, which means their symptoms look quite similar. Your website will get slower and may crash.
You can easily find out whether it is a brute force attack or a DDoS attack by looking at the Sucuri plugin’s login reports.
Simply install and activate the free Sucuri plugin and then go to the Sucuri Security » Last Logins page.
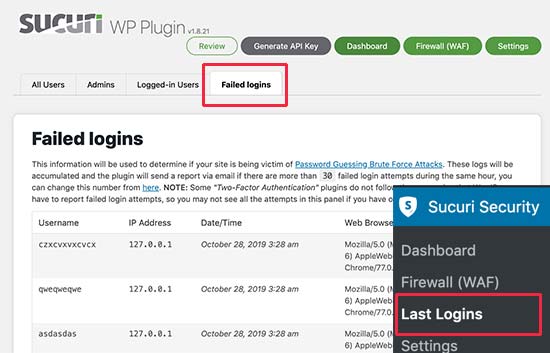
If you are seeing a large number of random login requests, then this means your wp-admin is under a brute-force attack. To stop it, you can see our guide on how to block brute force attacks in WordPress.
What to Do During a DDoS Attack
DDoS attacks can happen even if you have a web application firewall and other protections in place. Companies like CloudFlare and Sucuri deal with these attacks on a regular basis, and most of the time, you will never hear about them since they can easily mitigate them.
However, in some cases, when these attacks are large, they can still impact you. In that case, it’s best to be prepared to mitigate the problems that may arise during and after the DDoS attack.
Following are a few things you can do to minimize the impact of a DDoS attack.
1. Alert Your Team Members
If you have a team, then you need to inform co-workers about the issue.
This will help them prepare for customer support queries, look out for possible issues, and help out during or after the attack.
2. Inform Customers About the Inconvenience
A DDoS attack can affect the user experience on your website. If you run a WooCommerce store, then your customers may not be able to place an order or log in to their accounts.
You can announce through your social media accounts that your website is having technical difficulties and everything will be back to normal soon.
If the attack is large, then you can also use your email marketing service to communicate with customers and ask them to follow your social media updates.
If you have VIP customers, then you might want to use your business phone service to make individual phone calls and let them know how you are working to restore the services.
Communication during these tough times makes a huge difference in keeping your brand’s reputation strong.
3. Contact Hosting and Security Support
Get in touch with your WordPress hosting provider. The attack on your site may be part of a larger attack targeting their systems. In that case, they will be able to provide you with the latest updates about the situation.
Contact your firewall service and let them know that your website is under a DDoS attack. They may be able to mitigate the situation even faster and provide you with more information.
With firewall providers like Sucuri, you can also set your settings to be in ‘Paranoid Mode’, which helps block a lot of requests and make your website accessible for normal users.
How to Keep Your WordPress Website Secure
WordPress is quite secure out of the box. However, as the world’s most popular website builder, it is often targeted by hackers.
Luckily, there are many security best practices that you can apply to your website to make it even more secure.
We have compiled a complete step-by-step WordPress security guide for beginners. It will walk you through the best WordPress security settings to protect your website and its data against common threats.
You might also like to see some other articles related to improving your WordPress security:
- How to Perform a WordPress Security Audit (Complete Checklist)
- Best WordPress Security Plugins to Protect Your Site (Compared)
- Best WordPress Security Scanners for Detecting Malware and Hacks
- How to Scan Your WordPress Site for Potentially Malicious Code
- Top Reasons Why WordPress Sites Get Hacked (& How to Prevent It)
- How to Protect Your WordPress Site From Brute Force Attacks
- How to Find a Backdoor in a Hacked WordPress Site and Fix It
- How to Monitor User Activity in WordPress with Security Audit Logs
- How to Add HTTP Security Headers in WordPress (Beginner’s Guide)
We hope this article helped you learn how to block and prevent a DDoS attack on WordPress. You may also want to see our guide on how to prevent WordPress SQL injection attacks and our essential checklist of crucial WordPress maintenance tasks to perform regularly.
If you liked this article, then please subscribe to our YouTube Channel for WordPress video tutorials. You can also find us on Twitter and Facebook.




Dennis Muthomi
I’ve had great results using Sucuri on my clients’ sites – it really works!
Here’s a quick tip from my experience: Don’t forget to keep your plugins and themes updated. Outdated plugins/themes can be a weak spot during attacks.
I’ll definitely be passing these security tips along to my clients. It’s super important to stay on top of WordPress security and not end up in problems later on.
Olaf
Prevention is always fundamental. I often investigate what DDoS solutions the web provider itself has. They often have great and expensive automated software that can detect these attacks right from the start. Another excellent solution is CloudFlare. They are simply the best on the market for this. When I occasionally hear about the massive attacks they have filtered from news, I know that my website is always safe with them.
Oyatogun Oluwaseun Samuel
Thank you so much for this insight about DDoS attack. Being able to differentiate between DDoS and Brute force is one of the key steps to proffer solution which the Sucuri plugin will help you with. The Sucuri plug is usually recommended for wordpress security if you’re a small business as it is affordable you can then up grade to Cloudfare which in my opinion offer superior service. Also using hosting service specific to Wordpress is also beneficial as most of hemhave system in place to guide against security issues that may affect your Wordpress site.
Mrteesurez
Helpful article, I have learnt and understood what DDoS attack is and how to stop and prevent them on website but how can a some say whether it’s a brutal force or DDoS attack when he has not been using any firewall plugin ?
WPBeginner Support
Your hosting provider can help narrow down what type of attack was affecting your site.
Admin
Jiří Vaněk
Currently, I dare to say that an excellent and free protection against DDoS attacks is Cloudflare. The DNS A record is hidden behind a proxy DNS, so the attack is mostly directed not at the target server but at the Cloudflare server. Cloudflare then effectively filters out the DDoS attack. For me, currently one of the best solutions available.
Prabuddh
Disable XML RPC in WordPress Code is wrong,
The code ends with but you ended with which gives an error, Please solve this.
Thanks
WPBeginner Support
We di bit see your recommendations in your comment but we did find a typo and it should be fixed
Admin
Mohamad EL-Wakeel
great articles, but would you make one as comparison between
DDoS Attack & Brute Force Attack, and how to detect both.
Thanks.